In This Article
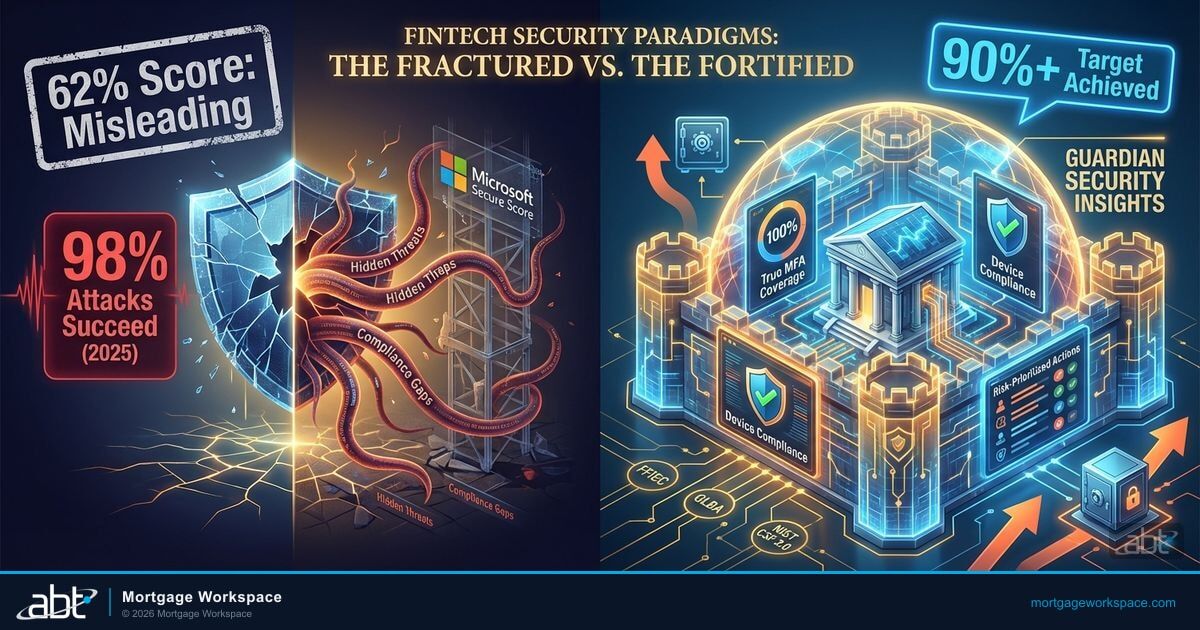
Microsoft Secure Score tells you 62%. Microsoft doesn't attach letter grades to that number, but your executive team hears "passing grade" and calls it a B. Your auditor hears "38% of recommended security controls are not implemented" and calls it a finding. And by traditional grading, where 60-69% is a D, 62% isn't a B at all. Same number, three different conclusions, and this is exactly the disconnect that gets mortgage lenders into trouble.
"Secure Score grades on a curve. A passing grade at your board meeting is a failing grade at your state examiner's table. And the loan origination system your score doesn't see is the surface your attacker is already scanning."
ABT security program framing for mortgage operations
Secure Score is a useful starting point. It is not a security strategy. It rewards easy wins over hard controls. It does not map to the regulatory frameworks that govern mortgage lenders, credit unions, and banks. And it does not tell you whether your operation is actually protected against the threats that matter to a lender moving borrower data across an LOS, a point-of-sale portal, and a servicing platform every hour of every business day.
Guardian Security Insights starts where Secure Score stops. It uses the score as one input among many, sets a 90%+ target across all four categories, and wraps the number in operational context that turns a metric into a security program, one that recognizes mortgage operations as a distinct regulatory and threat environment.
The Problem with Grading on a Curve
Microsoft Secure Score calculates a percentage based on how many recommended actions your tenant has implemented across four categories: Identity, Data, Devices, and Apps. It sounds straightforward. The problems are in the details, and for mortgage companies the details are where borrower data lives.
The Score Rewards Low-Hanging Fruit
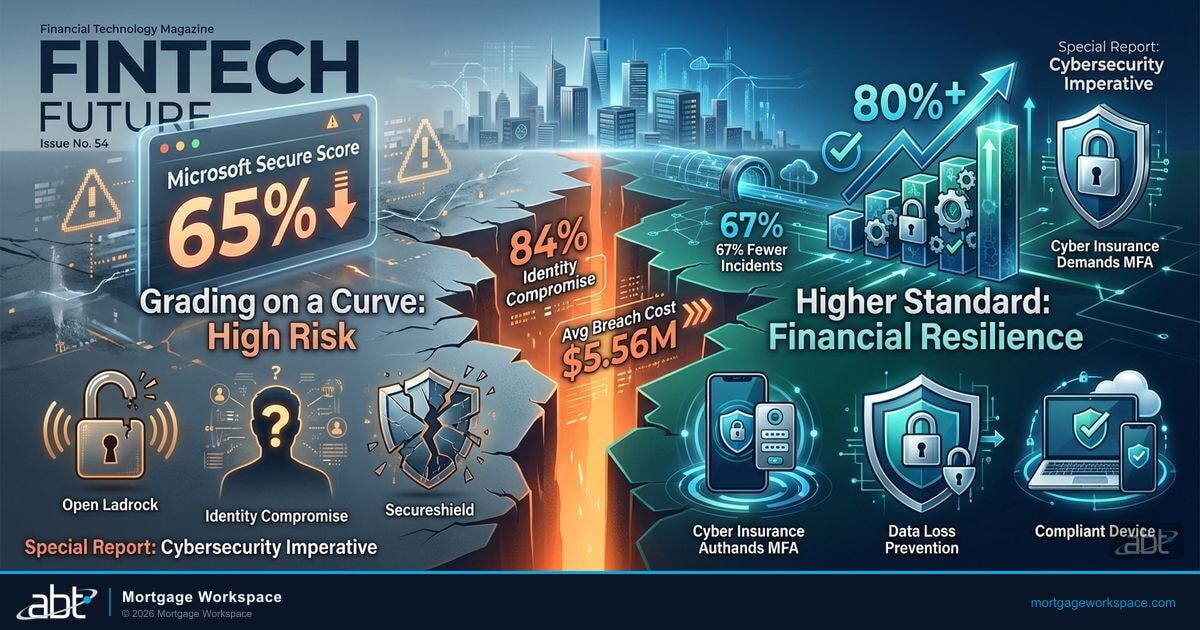
Some Secure Score actions are worth more points than others. The weighting does not always reflect actual risk. A mortgage lender can reach 65% by implementing a dozen easy changes while leaving the hard ones (device compliance for branch loan officers, DLP enforcement on NPI, Conditional Access for every role that touches Encompass or an LOS) untouched. The score goes up. The actual risk stays the same. And the actual risk is where CFPB, state regulators, and your warehouse line provider look first.
The Comparison Is Misleading
Microsoft shows how your score compares to "similar organizations." But "similar" is based on tenant size and industry tags, not regulatory profile. A mortgage lender holding borrower Social Security numbers, tax returns, and bank statements has a different threat model than a marketing agency with the same user count. The comparison creates false comfort, right up until a loan officer clicks the wrong link and the same SharePoint site that felt compliant becomes an incident report.
The Score Does Not Map to Mortgage Compliance
No regulator accepts Secure Score as compliance evidence. The CFPB enforces Regulation Z, Regulation X, and the GLBA Safeguards Rule with specific documented controls. State mortgage regulators, the FTC Safeguards Rule, and GSE seller-servicer guides (Fannie Mae, Freddie Mac, Ginnie Mae) all require evidence that maps to their frameworks, not to Microsoft's recommended actions. Secure Score measures Microsoft's recommended actions. The overlap is significant but not complete. And the gaps are exactly where examiners live.
The Score Is a Snapshot, Not a Trend
Secure Score shows today's number. It does not show last Tuesday's number, or the fact that someone created a Conditional Access exclusion on Wednesday that dropped your Identity score by 8 points the same week a processor opened an LOS vendor integration via an app password. Without trend data and change tracking, a good score today can mask a deteriorating trajectory. And for mortgage lenders, a deteriorating trajectory between audits is how regulatory findings become consent orders.
Why This Matters Right Now for Mortgage Operations
The IBM X-Force Threat Intelligence Index 2026 found valid account credentials accounted for 32% of all initial access vectors in 2025. Exploitation of public-facing applications surged 44% to become the single largest entry point. Check Point's Cyber Security Report 2026 found organizations faced an average of 1,968 cyberattacks per week in 2025, a 70% increase since 2023. Your Secure Score may say MFA is enabled. The threat landscape says attackers have moved to the credentials, tokens, and session data that bypass MFA entirely. And mortgage borrower portals, LOS login pages, and servicing dashboards are the public-facing applications that surge is hitting.
What Mortgage Operations Actually Need
Mortgage IT teams need a security operating model that answers three questions every day:
- What changed since yesterday? New risks, policy modifications, enrollment gaps, device compliance changes, including anything that affects data flowing into or out of the LOS, the POS, the CRM, and the servicing platform.
- What should we fix first? Prioritized by actual risk to the lender, not by Secure Score point value.
- Can we prove it to our regulators, our investors, and our warehouse line? Evidence that maps to GLBA Safeguards, CFPB, state mortgage regulators, FinCEN BSA, FHFA/GSE seller-servicer requirements, and cyber insurance underwriting.
Secure Score partially answers question two. Guardian Security Insights answers all three. For mortgage companies navigating a tightening GSE compliance posture and an accelerating threat landscape, a metric without operational context is not a security program.
How Guardian Security Insights Goes Beyond the Score
Category-Level Visibility with Operational Context
Guardian Security Insights breaks Secure Score into its four components (Identity, Data, Devices, Apps) and adds operational context to each. A score of 75% in Identity means something different depending on whether the remaining 25% is legacy authentication used by a legacy LOS connector (critical risk) or a cosmetic setting like login page branding (minimal risk).
For each category, Guardian Security Insights shows:
- Current score and 30/60/90-day trend
- Specific unimplemented actions ranked by actual risk, not point value
- Estimated effort and impact for each action
- Regulatory mapping (which framework requires this control: GLBA, CFPB, state mortgage regulator, GSE seller-servicer guide, NYDFS 500.11 where applicable)
Your IT team sees the same data Microsoft provides, organized by what matters to a regulated mortgage lender instead of what matters to Microsoft's scoring algorithm.
MFA Coverage That Tells the Truth
Secure Score checks whether MFA is "enabled." Guardian Security Insights checks whether MFA is completed. The distinction matters enormously when a loan officer class of 14 new hires lands on a Monday.
A user who started MFA registration but never finished shows as "enabled" in the Microsoft admin portal and counts toward your Secure Score. But that user has no second factor protecting their account. They are as vulnerable as someone with no MFA at all. For mortgage lenders where new hire cohorts move fast and contractor accounts spin up for a single refi boom, the gap between MFA-registered and MFA-enforced has real consequences.
Guardian Security Insights identifies every user in this gap state. For the mortgage companies ABT manages, this gap typically affects 5-15% of the user base at any given time, heavier in quarters when a pipeline surge drives onboarding velocity past the IT team's ability to keep up. Those users are the ones attackers will find first.
Stale Account Detection That Connects to Cost
Secure Score does not track stale accounts. Guardian Security Insights does. An account that has not been used in 90 days is a risk (credentials can be compromised without anyone noticing) and a cost (the license is still being paid for). For mortgage lenders, stale accounts are not an abstract problem. They are usually a specific one, and it is usually the same one: a loan officer or processor who left during a reduction in force, a refi-boom contractor whose term ended, or a branch that was consolidated and never cleaned up.
For a 300-user mortgage lender, stale accounts typically sit at 8-12% of the user base. That's 24 to 36 accounts nobody is using, and the lender is still paying for all of them. At $22 per user per month for Business Premium, that's $6,336 to $9,504 per year in licenses tied to inactive accounts that are also security liabilities (dormant credentials get compromised without anyone noticing, and when the attacker logs in as a former loan officer, the tenant's Conditional Access doesn't flag it because "the account exists").
Guardian Security Insights surfaces stale accounts in the nightly scan with the specific account names, last login dates, assigned licenses, and, for mortgage lenders. The LOS, POS, and CRM applications that account was connected to. Your team can disable the accounts, revoke sessions, and reclaim the licenses in the same action. That last part matters: a former processor's account disabled in Entra ID is not the same as that processor's session tokens revoked across every mortgage-adjacent app they ever signed into.
Device Compliance Beyond Enrollment
Secure Score measures whether Intune is configured. Guardian Security Insights measures whether devices are actually compliant. A mortgage lender tenant with Intune enabled but 40% of devices failing compliance checks looks good on Secure Score and terrible on the ground, particularly when those 40% include branch laptops that access Encompass and personal devices that process commissions.
Guardian Security Insights tracks device compliance rates daily. It identifies devices running outdated operating systems, missing encryption, or failing to report to Intune. For mortgage companies where every device accesses borrower NPI, GLBA-regulated loan data, and tax returns, device compliance is not optional. Running a structured Conditional Access review reveals the specific gaps that Intune enrollment counts do not surface, legacy branch devices, personal devices in a BYOD overflow, or third-party LOS vendor machines that inherit your tenant's access on shared sessions.
Compliance Evidence as a Byproduct
Mortgage operations answer to a patchwork of regulators, and that patchwork is exactly why Secure Score alone fails as compliance evidence. A single mortgage lender or servicer typically has to satisfy:
- GLBA Safeguards Rule. Non-bank mortgage companies are covered "financial institutions" under the FTC's Safeguards Rule. The rule requires a written information security program, access controls, encryption of NPI at rest and in transit, MFA for access to customer information, a qualified individual overseeing the program, and breach notification for NPI events affecting 500 or more consumers.
- CFPB Regulations Z and X. Truth in Lending Act and RESPA rules shape borrower-facing disclosure handling and servicing communications. Note on Section 1033: the CFPB's Open Banking rule was issued October 2024 and stayed on October 29, 2025 by a Kentucky federal court. The first compliance tier covers bank and credit union deposit-account data, not mortgage data. For mortgage operations, the posture is watch and prepare, not remediate to a deadline that currently does not exist.
- FinCEN BSA and SAR obligations. Non-bank mortgage lenders and originators have AML program and Suspicious Activity Report duties. FinCEN's FY2024 report recorded 4.7 million SAR filings, with cyber-enabled SARs up 12.4% year over year. Wire fraud and loan fraud in the mortgage pipeline are routinely cyber-enabled.
- NYDFS 23 NYCRR Part 500. Applies to every Covered Entity licensed under New York banking law, including mortgage bankers, originators, and servicers holding a NY license. The final compliance wave landed November 1, 2025: universal MFA, third-party service provider MFA verification, annual risk assessments, and 72-hour incident notification. The Bayview Loan Servicing $20M multistate settlement is the clearest recent reminder that enforcement here has teeth.
- GSE Seller/Servicer Guides. Fannie Mae's August 12, 2025 Selling Guide update introduced a 36-hour cyber incident notification requirement and 14 Approved Critical Domains for secure data transmission. Freddie Mac's Single-Family Seller/Servicer Guide Section 1302 requires documented information security and business continuity programs, with SOC 2 Type 2 audits mandatory for larger seller-servicers; Bulletin 2025-16 (effective March 3, 2026) added AI use documentation and governance requirements. Ginnie Mae APM 24-02 set a 48-hour cyber incident notification standard in 2024 alongside the Cybersecurity Acknowledgement and Provisioning System (CAPS) attestation and Cybersecurity Acknowledgement Agreement.
- State mortgage regulators and NMLS. Varies by state. NYDFS 500 remains the most stringent. Contrary to common assumption, California's DFPI does not currently have a standalone Part-500-equivalent cybersecurity regulation. Most other state mortgage regulators defer to federal minimums and NMLS guidance rather than imposing standalone cyber rules.
- MBA and MISMO data security guidance. Industry standards around NPI classification, encryption, third-party vendor oversight, and incident response. Not mandatory, but used as audit baselines by investors, warehouse line providers, and cyber insurance underwriters.
Guardian Security Insights maps every nightly finding to the relevant framework. When a CFPB examiner asks for proof of MFA coverage, the evidence is tagged. When a warehouse line provider asks about Conditional Access for borrower-facing applications, the report is indexed. When a GSE asks for documentation aligned to a specific Seller/Servicer Guide section, the control evidence is organized that way. That is the difference between a score and a program: the score gives you a number, and the program tells you where the number comes from and who it satisfies.
ABT manages Microsoft 365 tenants for 750+ financial institutions on Guardian, including mortgage lenders, servicers, credit unions, and community banks. The MFA gap Secure Score misses most often is incomplete enrollment: users who started registration but never finished the second factor. Guardian Security Insights flags those users the night they appear so remediation happens before an attacker gets there first.
Your Secure Score Says Green. Your Auditor Disagrees.
A Security Grade Assessment shows what's behind the number, including the MFA, stale account, and third-party integration gaps a mortgage tenant's Secure Score won't surface.

The Credential Crisis Scores Can't See
The threat landscape has shifted underneath point-in-time scoring. While Secure Score rewards MFA enablement, attackers have moved to credential harvesting at industrial scale. And mortgage operations are a particularly rich target because borrower portals are public-facing by design and loan officers log into a dozen adjacent systems every day.
IBM X-Force Threat Intelligence Index 2026 found infostealers harvested credentials at unprecedented scope, including over 300,000 AI service account credentials advertised on dark web markets in 2025 alone. Valid account credentials remained a top-two initial access vector, accounting for 32% of all tracked intrusions in the year. Check Point's Cyber Security Report 2026 found organizations worldwide faced an average of 1,968 cyberattacks per week in 2025, a 70% increase since 2023.
For mortgage lenders, servicers, and warehouse line participants, this means the MFA checkbox in Secure Score is necessary but nowhere near sufficient. The question isn't "Is MFA enabled?" The questions are:
- Are any loan officers, processors, or closers stuck in registration-started-but-not-completed MFA states?
- Are Conditional Access policies catching token replay and adversary-in-the-middle attacks targeting borrower portals?
- Are former loan officers' credentials still active in the tenant after the last RIF?
- Are service accounts used by LOS, POS, and servicing platform integrations using app passwords that bypass MFA entirely?
- Are devices accessing the tenant from IP ranges outside your approved branch and remote-work footprint?
Guardian Security Insights answers these questions in its nightly scan. Secure Score doesn't ask them. Neither does the static mortgage lender security checklist that gets dusted off before an annual review and set down the moment the finding is cleared.
The 90% Target and Why It Matters
ABT targets 90% or higher Secure Score across all four categories for every managed tenant. Most mortgage lenders start between 35% and 55%.
The 90% target is not arbitrary. It represents a posture where:
- Legacy authentication is blocked (stops 99% of password spray attacks. The attack class that most often targets loan officers via the login pages for LOS, POS, and borrower portals)
- MFA is fully enrolled for all users, not just registered
- All devices (branch, remote, and BYOD) meet compliance policies
- DLP policies protect NPI, borrower financial data, and tax returns against accidental external share
- Email authentication (SPF/DKIM/DMARC) prevents spoofing. The foundation every wire fraud prevention program depends on
- Conditional Access restricts access by location, device, and risk level. And covers the role types (loan officer, processor, closer, servicing rep, warehouse line admin) that see the most attack traffic
The remaining 10% typically consists of controls that require trade-offs: settings that would break specific workflows, controls that duplicate coverage from other tools, or Microsoft recommendations that do not apply to the lender's environment.
Cyber insurance carriers now factor Secure Score into underwriting. For mortgage lenders, who carry higher-than-average E&O and cyber premiums because of the NPI volume, demonstrating 90%+ in MFA and Data Protection can reduce premiums. Guardian Security Insights gives your CFO the documentation to make that case during renewal negotiations.
"Financial services was the most-breached industry for the second consecutive year in 2025. The mortgage operations that survived without headline-making incidents weren't the ones with the highest scores. They were the ones with actual security programs, and they knew which part of their LOS, POS, and servicing stack was the next soft spot before the attacker did."
Analysis based on ITRC 2025 Annual Data Breach Report
From Score to Security Program
Secure Score is a number. A security program is a discipline. The difference shows up in how your mortgage operation handles the unexpected.
When a new vulnerability is disclosed, a score-focused team checks whether it affects their Secure Score. A program-focused team checks whether it affects their loan officers, borrower data, and compliance posture, including whether it rides in on a third-party integration the team forgot was still provisioned. Guardian Security Insights provides the visibility for the second approach.
When a third-party vendor is breached, an LOS, a POS, a credit pull provider, a servicing vendor, or an AI tool, a score-focused team has no immediate action items. A program-focused team checks their Conditional Access policies, reviews third-party application permissions, and verifies that the breach did not affect their tenant. Guardian Security Insights surfaces this information without requiring your team to know where to look. The FHFA Anthropic episode is a recent example of exactly how fast third-party AI vendor posture can flip from "approved" to "terminate the contract", and of how little most mortgage IT teams can surface about their current exposure in the hour that decision lands.
When a regulator updates their requirements, CFPB Section 1033 tier deadlines, a state mortgage regulator cyber update, a GSE Selling Guide revision, or an NYDFS 500.11 effective date, a score-focused team starts a new compliance project. A program-focused team checks their existing controls against the new requirements and finds they already meet most of them because they built the program on fundamentals, not point-chasing.

ABT's Architecture Advantage
ABT runs a pure Microsoft technology stack. No ConnectWise. No Kaseya. No SolarWinds. No third-party MSP platforms. Guardian Security Insights is built on the same Microsoft tools your mortgage operation already licenses: Entra ID, Intune, Defender, Purview, and Sentinel.
This matters for going beyond Secure Score because the data sources are native. Guardian Security Insights reads directly from Microsoft's APIs. There is no translation layer, no third-party data warehouse, no secondary sync that introduces lag or data loss. The findings are as current as the data in your tenant. Which is exactly what you want when a warehouse line provider or a GSE asks for proof of your security posture inside a single-hour SLA.
ABT serves 750+ financial institutions, and mortgage lenders and servicers are a primary vertical inside that footprint. That scale means the Guardian team has tuned its scanning, prioritization, and remediation guidance across thousands of tenants. The recommendations your team receives are informed by patterns across the largest financial institution MSP client base in the market, including mortgage-specific configurations for Encompass integrations, POS platforms, borrower portals, and servicing-side tooling, not generic guidance drawn from cross-industry averages.
Your Score Is Not Your Security
A number on a dashboard tells you where you stand. A managed security program tells you where you're going and how to get there. See what Guardian Security Insights reveals about your mortgage Microsoft 365 environment that Secure Score can't, including the loan officer, LOS, and servicing-platform gaps the score is silent on.
Frequently Asked Questions
Secure Score measures implementation of Microsoft's recommended actions, not the specific controls mortgage regulators require. No regulator accepts Secure Score as compliance evidence. Mortgage lenders answer to the GLBA Safeguards Rule (written security program, NPI encryption, MFA for customer information access, qualified individual, breach notification at 500+ consumers), CFPB Regulations Z and X, FinCEN BSA and SAR obligations for non-bank mortgage originators, NYDFS 23 NYCRR Part 500 where applicable, FHFA/GSE seller-servicer requirements (Fannie Mae's 36-hour notification plus 14 Approved Critical Domains, Freddie Mac Section 1302 and Bulletin 2025-16, Ginnie Mae APM 24-02 48-hour notification), and state mortgage regulator rules. Guardian Security Insights maps its nightly scan results to each of these frameworks, turning security monitoring data into audit-ready compliance documentation for examiners, GSE reviewers, warehouse line providers, and cyber insurance underwriters.
ABT targets 90% or higher across all four Secure Score categories for every managed tenant. Most mortgage lenders start between 35% and 55%. The 90% target represents full legacy auth blocking, complete MFA enrollment, device compliance enforcement across branch and remote users, active DLP policies protecting borrower NPI, and Conditional Access enforcement that covers loan officer, processor, closer, and servicing roles. Cyber insurance carriers factor Secure Score into underwriting decisions, and mortgage lenders often see premium impact because of the elevated NPI volume.
Secure Score counts users as MFA-enabled once registration begins. Guardian Security Insights distinguishes between MFA-registered and MFA-enrolled. Loan officers, processors, or contractors who started setup but never completed the second factor appear compliant in Microsoft dashboards while remaining unprotected. Guardian Security Insights identifies this gap in nightly scans, typically affecting 5-15% of users in mortgage lender tenants, with higher rates during refi-boom onboarding surges.
The CFPB issued the Section 1033 Final Rule in October 2024, requiring covered data providers to make consumer financial data available to authorized third parties with consumer consent. On October 29, 2025, a Kentucky federal court stayed the rule. The first compliance tier covers bank and credit union checking, savings, and transaction-account data; mortgage data is not included at this stage. For mortgage lenders, the operational posture is watch and prepare rather than remediate to an imminent deadline. The existing GLBA Safeguards Rule continues to govern NPI protection in the meantime, and any future expansion of Section 1033 to mortgage servicing or origination data will map to authentication, access control, and third-party integration logging requirements that Guardian Security Insights already surfaces nightly, strong MFA on authorized third-party connections, token and session controls on consumer-facing data APIs, and the audit trail a 1033-style authorized data sharing regime will require when it arrives.
Yes. Fannie Mae's Selling Guide update on August 12, 2025 requires sellers and servicers to notify Fannie Mae within 36 hours of a confirmed cyber incident affecting loan-level data, and restricts secure data transmission to 14 Approved Critical Domains (ACD). Freddie Mac's Single-Family Seller/Servicer Guide Section 1302 mandates documented information security and business continuity programs, with annual SOC 2 Type 2 audits for larger mortgage servicers; Bulletin 2025-16, effective March 3, 2026, added artificial intelligence use documentation and governance requirements. Ginnie Mae's All Participant Memorandum 24-02 established a 48-hour cyber incident notification standard for issuers in 2024, alongside the Cybersecurity Acknowledgement and Provisioning System (CAPS) attestation process and the Cybersecurity Acknowledgement Agreement. Each of these requirements calls for specific documented controls, access control, encryption, monitoring, incident response, and third-party oversight, that map directly to the categories Guardian Security Insights reports against. The nightly scan produces the evidence a seller-servicer needs when a GSE reviewer asks for it, aligned to the specific Guide section the question falls under.
Yes. NYDFS 23 NYCRR Part 500 applies to every Covered Entity licensed under New York banking, insurance, or financial services law, including mortgage bankers, mortgage originators, and mortgage servicers that hold a NY license. The final compliance wave landed November 1, 2025 and introduced universal MFA for all individuals accessing information systems, MFA verification for third-party service providers with access to the Covered Entity's nonpublic information, annual cybersecurity risk assessments, and 72-hour incident notification. The Bayview Loan Servicing $20M multistate settlement is a recent reminder that mortgage servicers face material enforcement exposure under state cyber laws. California does not currently have a Part-500-equivalent cybersecurity regulation at the DFPI level, a common misconception worth flagging for mortgage operations that run across both states. Other state mortgage regulators generally follow federal and NMLS guidance rather than imposing standalone cyber rules. Guardian Security Insights documents MFA coverage, TPSP posture, Conditional Access, and change tracking in a format NYDFS auditors and state mortgage examiners can accept as contemporaneous evidence.
Yes. Cyber insurance carriers use Secure Score data during underwriting, and mortgage lenders see pointed scrutiny because of NPI volume and wire transfer exposure. Demonstrating high scores in MFA enforcement and Data Protection categories can reduce premiums. Guardian Security Insights tracks Secure Score trends with 30/60/90-day history and produces documentation that CFOs can present during insurance renewal negotiations to demonstrate security posture improvements over time.

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch built Guardian Security Insights to answer the question every regulated mortgage lender, credit union, and bank faces: what does your security posture actually look like beyond the score? With 750+ financial institutions under management, including a primary mortgage lender and servicer vertical, ABT's Guardian platform operationalizes the security program that Secure Score only measures, turning nightly scans into audit-ready evidence and daily compliance discipline across CFPB, FHFA/GSE, state mortgage regulators, and cyber insurance requirements.